2024-04-09 06:00:05
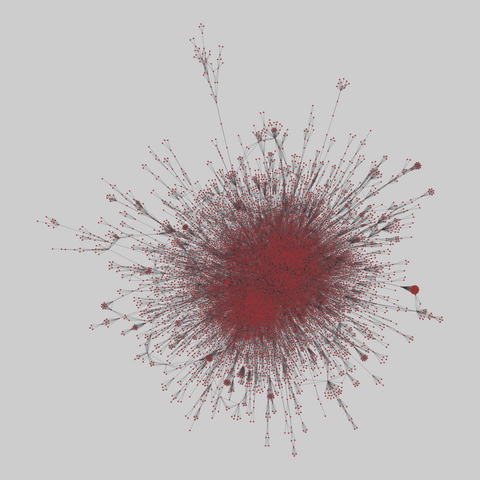
physics_collab: Multilayer physicist collaborations (2015)
Two multiplex networks of coauthorships among the Pierre Auger Collaboration of physicists (2010-2012) and among researchers who have posted preprints on arXiv.org (all papers up to May 2014). Layers represent different categories of publication, and an edge's weight indicates the number of reports written by the authors. These layers are one-mode projections from the underlying author-paper bipartite network.
This n…
2024-05-08 09:38:12
Researchers at German cybersecurity company Security Research Labs discovered that a vast network of fake shops originating in China touting designer brands took money and personal details from 800,000 people in Europe and US.
Chinese network behind one of world’s ‘largest online scams’
https://www.theguardian.com/money/article/2024/may/08/chinese-network-behind-one-of-worlds-largest-online-scams
2024-04-10 07:28:42
Combinational Nonuniform Timeslicing of Dynamic Networks
Seokweon Jung, DongHwa Shin, Hyeon Jeon, Jinwook Seo
https://arxiv.org/abs/2404.06021 https://
2024-04-08 07:19:07
TIM Red Team Research scopre un Bug di CSV Injection su Ericsson Network Manager (ENM)
https://poliverso.org/display/0477a01e-dbc7a77c-d77c63eea06823b8
TIM Red Team Research scopre un Bug di CSV Injection su Ericsson Network Manager (ENM) Nel contin…
2024-05-09 08:34:07
This https://arxiv.org/abs/2307.12833 has been replaced.
link: https://scholar.google.com/scholar?q=a
2024-04-10 04:42:31
A software engineer who transitioned into cybersecurity shares tips for success: Target specific cyber areas, obtain relevant certifications, have a robust and error-free resume, use LinkedIn for networking, be confident in interviews, thoroughly research the job and interviewers, and remain persistent. https://reddit.com/r/cybersecurity/comments/1bzz6xf/
2024-05-10 06:48:07
PLLM-CS: Pre-trained Large Language Model (LLM) for Cyber Threat Detection in Satellite Networks
Mohammed Hassanin, Marwa Keshk, Sara Salim, Majid Alsubaie, Dharmendra Sharma
https://arxiv.org/abs/2405.05469
2024-04-10 06:51:06
Unifying Low Dimensional Observations in Deep Learning Through the Deep Linear Unconstrained Feature Model
Connall Garrod, Jonathan P. Keating
https://arxiv.org/abs/2404.06106
2024-04-08 07:33:11
2024-02-10 01:00:05
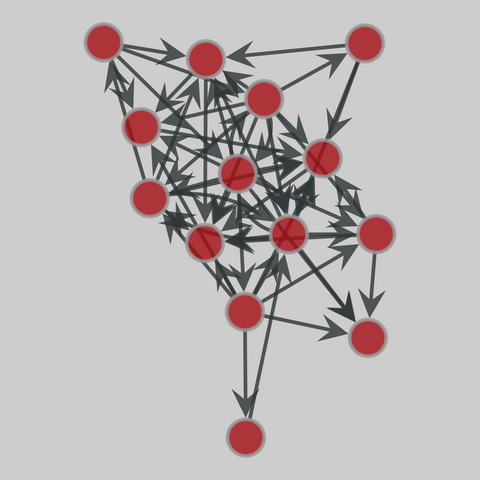
dom: Animal dominance archive (2022)
Animal dominance interaction data published over a century of research. The archive contains 434 agonistic interaction datasets, totaling over 241,000 interactions. A directed edge (i,j) corresponds to an antagonist interaction between i (winner) and j (loser). If a 'weight' edge property map exists, it counts the number of such interactions.
This network has 14 nodes and 54 edges.
Tags: Social, Animal, Weighted